Critical React2Shell flaw actively exploited in China-linked attacks
Multiple China-linked threat actors began exploiting the React2Shell vulnerability (CVE-2025-55182) affecting React and Next.js just hours after the max-severity issue was disclosed. [...]
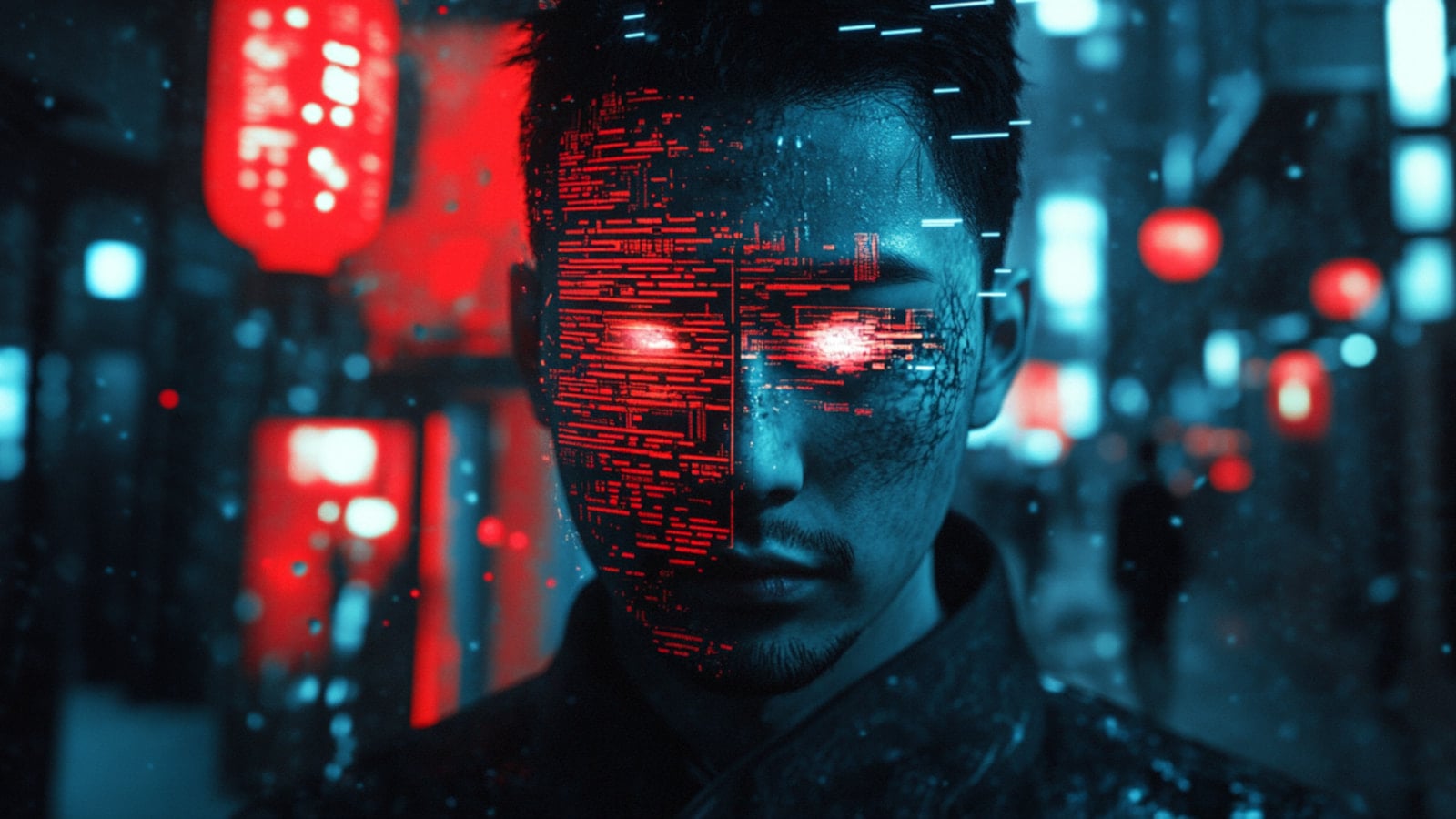
Multiple China-linked threat actors began exploiting the React2Shell vulnerability (CVE-2025-55182) affecting React and Next.js just hours after the max-severity issue was disclosed.
React2Shell is an insecure deserialization vulnerability in the React Server Components (RSC) 'Flight' protocol. Exploiting it does not require authentication and allows remote execution of JavaScript code in the server's context.
Related breach coverage
- AWS: China-linked threat actors weaponized React2Shell hours after disclosure2025-12-08
Multiple China-linked threat actors began exploiting the CVE-2025-55182, aka React2Shell flaw, within hours, AWS Security warns. Multiple China-linked threat actors began exploiting the CVE-2025-55182, also known as the React2Shell flaw, within hours, according to AWS Security. The researchers confirmed that this vulnerability doesn’t affect AWS services, however they opted to share threat intelligence data to […]
- New EtherRAT backdoor surfaces in React2Shell attacks tied to North Korea2025-12-10
NK-linked hackers are likely exploiting the React2Shell flaw to deploy a newly discovered remote access trojan, dubbed EtherRAT. North Korea–linked threat actors are likely exploiting the new critical React2Shell flaw (CVE-2025-55182) to deploy a previously unknown remote access trojan called EtherRAT, Sysdig researchers warn. The vulnerability CVE-2025-55182, is a pre-authentication remote code execution issue in React […]
- Chinese Hackers Exploiting React2Shell Vulnerability2025-12-05
AWS has seen multiple China-linked threat groups attempting to exploit the React vulnerability CVE-2025-55182. The post Chinese Hackers Exploiting React2Shell Vulnerability appeared first on SecurityWeek.
- Actively exploited critical flaw in Modular DS WordPress plugin enables admin takeover2026-01-16
A critical Modular DS WordPress flaw (CVE-2026-23550) is actively exploited, enabling unauthenticated privilege escalation. Threat actors are actively exploiting a critical Modular DS WordPress vulnerability tracked as CVE-2026-23550 (CVSS score of 10). Modular DS is a WordPress plugin with over 40,000 installs that helps manage multiple sites, enabling monitoring, updates, and remote administration. In plugin […]
